Back to Changelog
new release July 3, 2023
Security Context, Attack Path, Bulk Review, Remediation Your Way
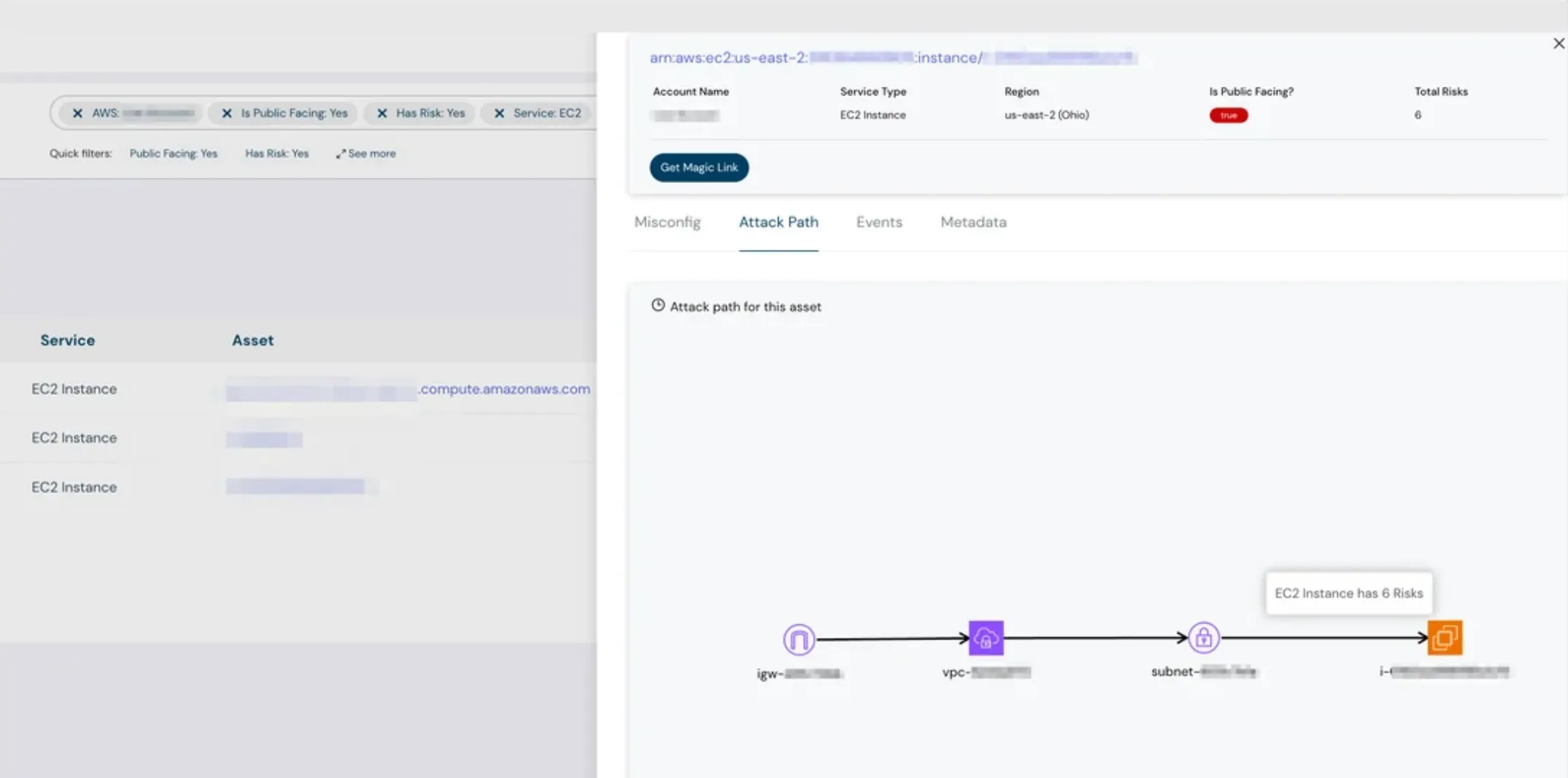
Attack Path for Compute & Database Resources
- Visually understand the relationships and risks affecting your compute and database resources.
- Correlates image vulnerabilities running in containers, helping you save productive time.
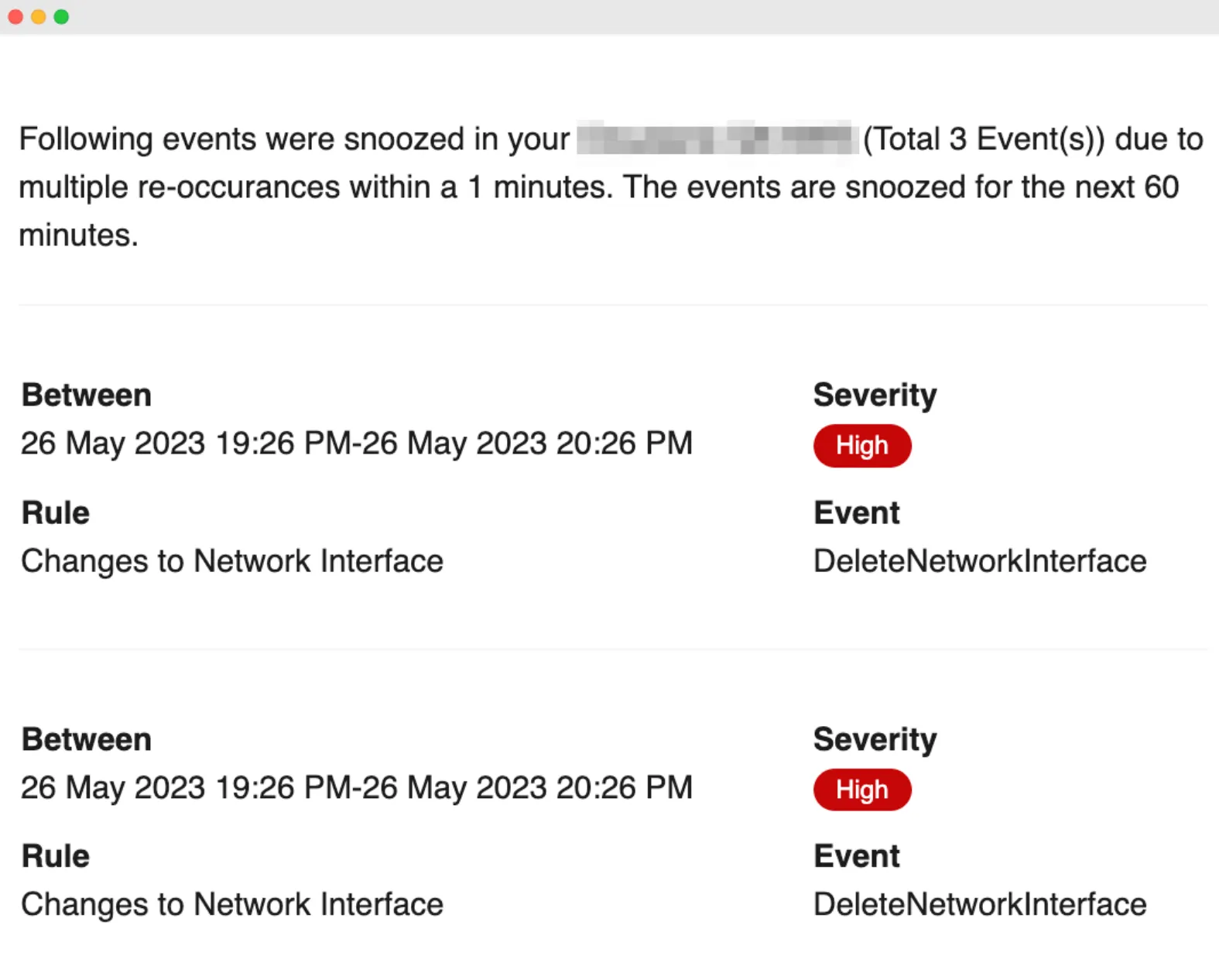
Event Auto-Snooze
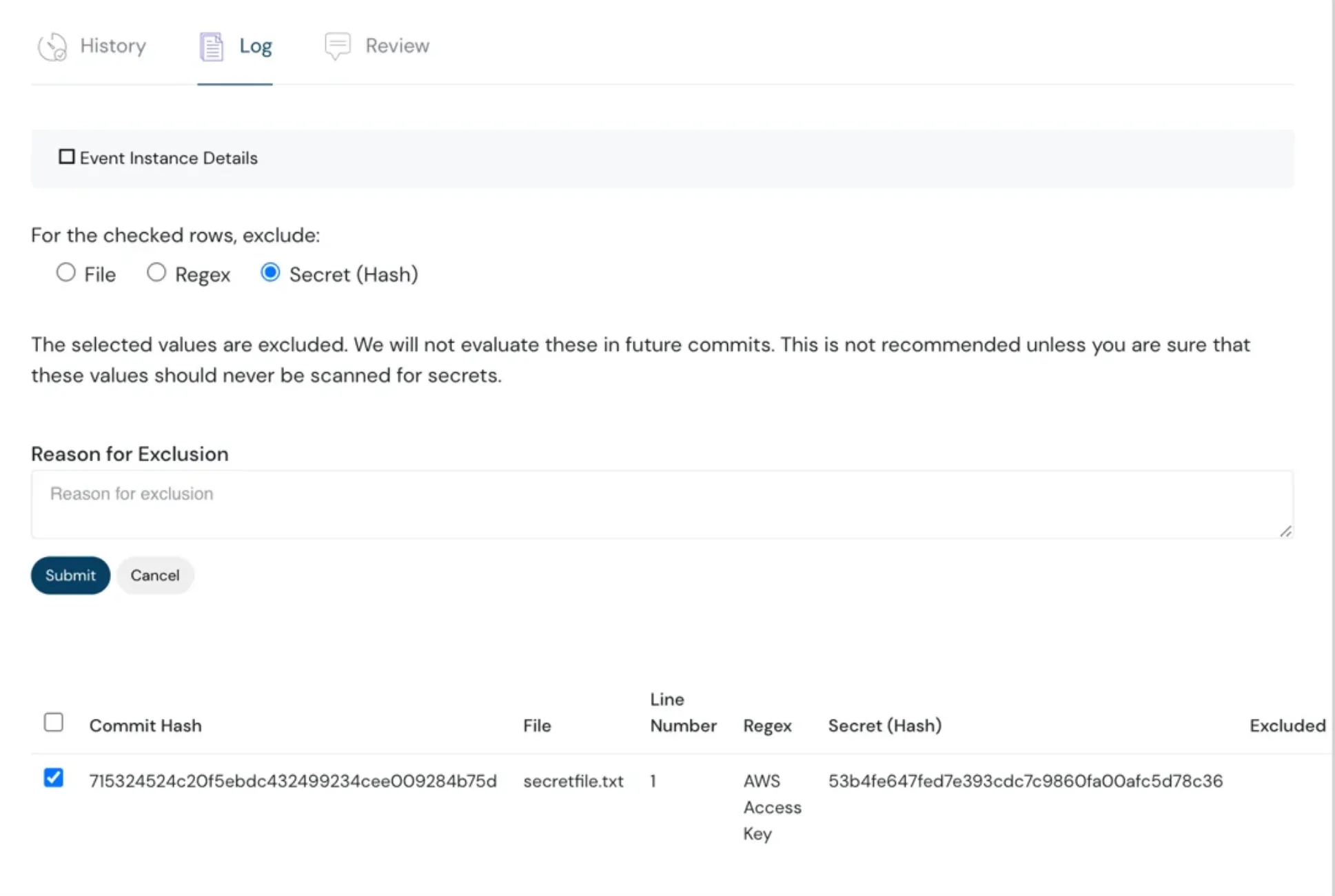
- Flexible identification and management of secrets within files or code repositories.
- Allows tailoring of the secret scanning process to match your organization’s needs.
Secret Scanning Capability
- Scan full repositories for secrets in both GitHub and Bitbucket.
- Detects and manages sensitive information before it can be exploited.
Bulk Event Review & Remediation
- Manage multiple events with a single action instead of updating each individually.
- Ideal for applying consistent changes across large numbers of events, reducing fatigue and saving time.
IAM Event Support for Azure
- Now includes additional event monitoring such as:
- Permissions updated for service accounts
- User MFA changes
Security for your Code, Cloud and Data
Cloudanix replaces your 5-6 disjointed security tools within 30 minutes.
Get StartedBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read MoreThursday, Feb 05, 2026
CSPM vs. CNAPP: Navigating Cloud Security Evolution for Modern Enterprises
The shift to cloud-native architectures represents a fundamental change in how applications are designed, built, and dep
Read MoreThursday, Jan 22, 2026
Top 10 Identity and Access Management Solutions
Identity and Access Management (IAM) has traditionally been considered one of the boring parts of security. But with the
Read More