Introducing the New Cloudanix Dashboard
We hope this year is off to a great start for you. Cloudanix is going through a lot of work to be as user-friendly as possible so that getting the security right doesn’t take all your time!
The month has just passed, and we have a brand NEW DASHBOARD!
What’s new this month?
We have had quite a change in the look and feel of our product. Here is what you should check out that has changed this month:
- Our Logo! Cloudanix has released its new and updated Logo!
- Our UX is better now. You can navigate through the dashboard much more easily.
- Last month we had released Container Security capability. In addition to k8s, we can also protect your k3s based workloads. Why should Edge workloads be left without security monitoring?
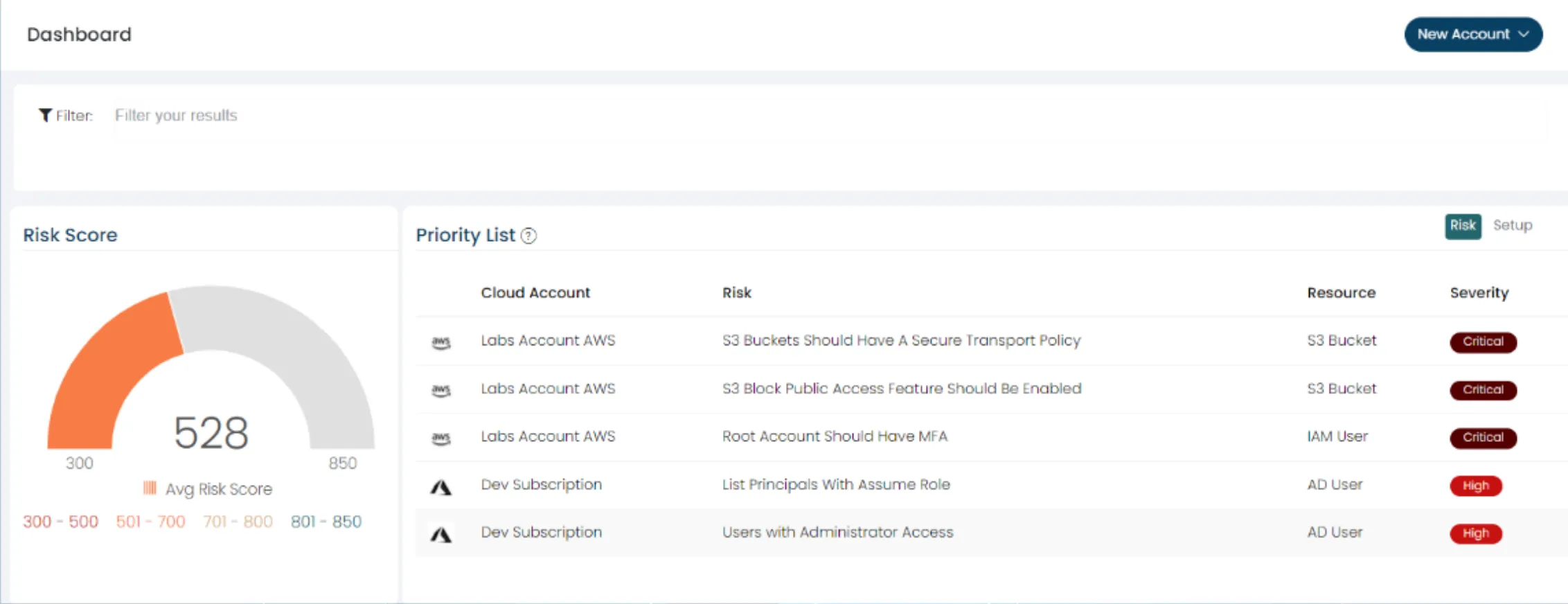
Take a quick look at how our Dashboard changed
Cloud security Software | Cloudanix
And also,
We would like to remind you that our Container Workload Protection (CWPP) is Live if you missed it last month!
TODO:// is not an option for Cloud Security
Security for your Code, Cloud and Data
Cloudanix replaces your 5-6 disjointed security tools within 30 minutes.
Get StartedBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read MoreThursday, Feb 05, 2026
CSPM vs. CNAPP: Navigating Cloud Security Evolution for Modern Enterprises
The shift to cloud-native architectures represents a fundamental change in how applications are designed, built, and dep
Read MoreThursday, Jan 22, 2026
Top 10 Identity and Access Management Solutions
Identity and Access Management (IAM) has traditionally been considered one of the boring parts of security. But with the
Read More