Increased productivity and visibility
Recently, several nations and businesses have been affected by data breaches, and according to statistics, human error accounts for 95 percent of cybersecurity breaches. This highlights how important it is for employees to be aware of the possible consequences that can protect their infrastructure from outside attacks.
In the past month, we have made significant progress on several new features and enhancements.
Here are some highlights
Container notification - Cloudanix dashboard
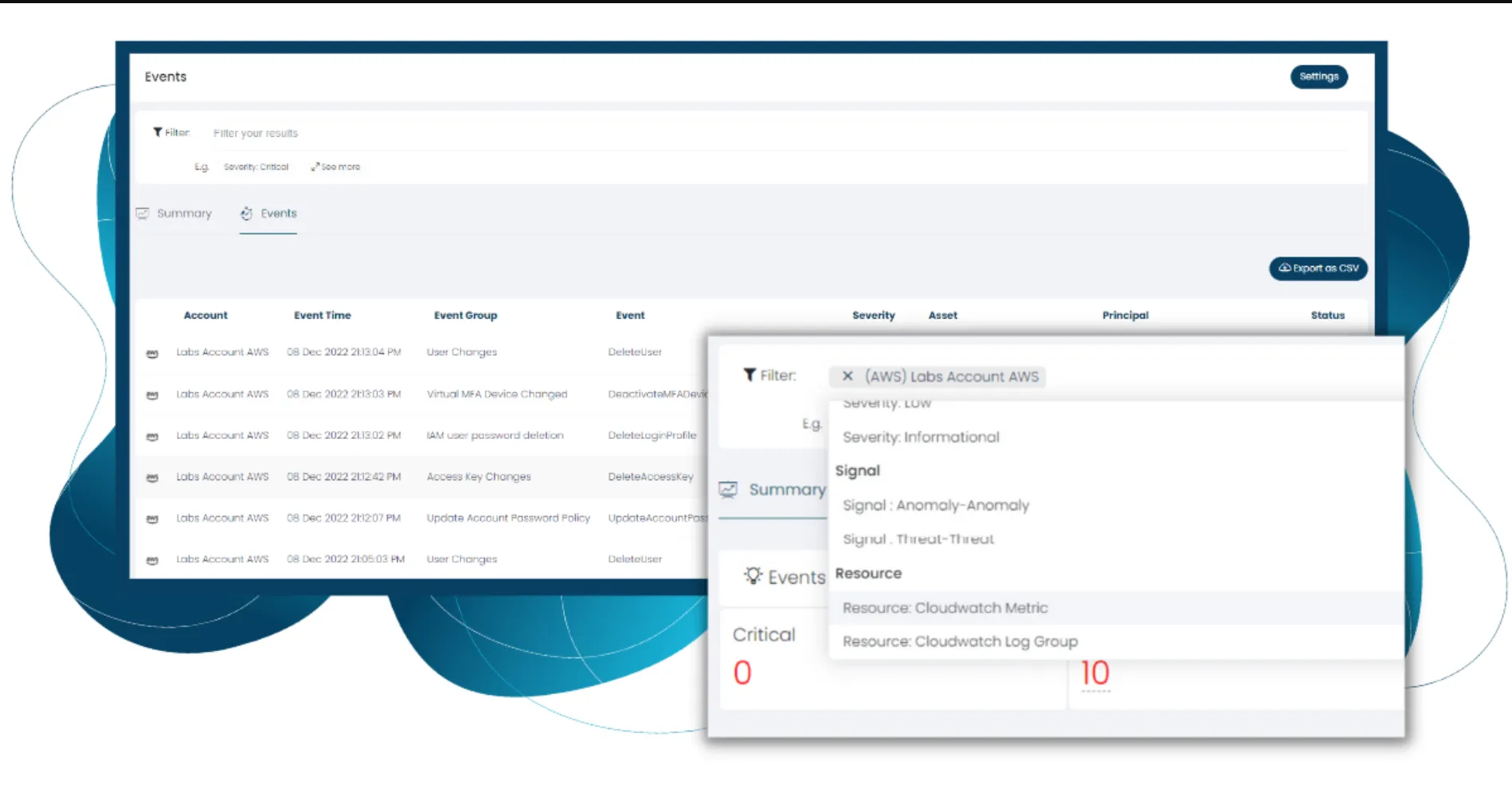
Predefined Views for focused work
With our pre-build views, customers can focus on the most important risks. Reach out to us to build more of these and we can roll them out for you. (shhhh .. we are soon rolling out an ability for you to build your own queries and views)
Enhanced Azure realtime monitoring
Additional rules supported, including events occurring in the Azure Active Directory. e.g Login without MFA, New role assignment as owner, etc.
IAM + Events
You can see the events initiated by the Principal right from the IAM screens.
Security for your Code, Cloud and Data
Cloudanix replaces your 5-6 disjointed security tools within 30 minutes.
Get StartedBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read MoreThursday, Feb 05, 2026
CSPM vs. CNAPP: Navigating Cloud Security Evolution for Modern Enterprises
The shift to cloud-native architectures represents a fundamental change in how applications are designed, built, and dep
Read MoreThursday, Jan 22, 2026
Top 10 Identity and Access Management Solutions
Identity and Access Management (IAM) has traditionally been considered one of the boring parts of security. But with the
Read More