GCP marketplace, secrets verification, SIEM integration and more
We’re excited to announce we are now listed on the GCP Marketplace too. We’re moving fast to not just provide better capabilities and workflows but to also make Cloudanix available at your favorite marketplaces like AWS, Azure and now GCP.
Read along to see what we have brewed for you last month.
Re-evaluate misconfiguration policies
Now, you can re-evaluate misconfiguration policies as soon as you address the gaps. No need to wait for end-of-the-day policy checks. And, you will get notified as soon as the evaluation is completed. Bonus: We also evaluate related policies.
 Cloudanix re-evaluation notification
Cloudanix re-evaluation notification
 Confirmation mail of the changes from Cloudanix dashboard
Confirmation mail of the changes from Cloudanix dashboard
Secrets verification
As part of secret detection in your SCM tool, Cloudanix can verify and check the validity of secrets checked-in in your code. Even by mistake!!
 Log of secrets checked in your code
Log of secrets checked in your code
SIEM integrations
Integrate security findings (Threats, Anomalies, Events, and Misconfigurations) with your favorite SIEM tool via webhooks.
Organization events
In AWS, Cloudanix can monitor organization level events and alert you when something suspicious occurs.
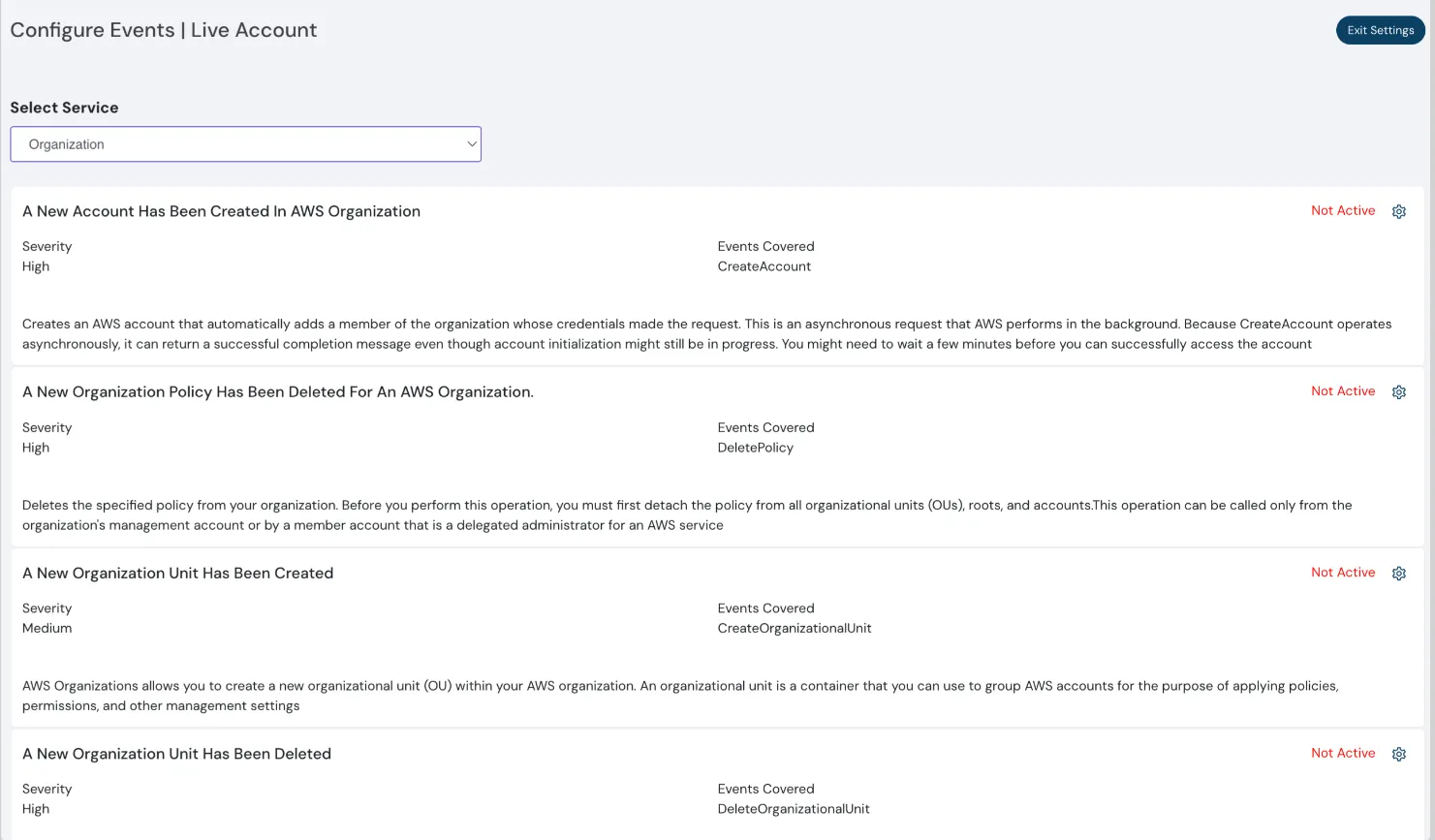
Log of secrets checked in your code
CIS 2.0.0 for GCP
We have added support for CIS 2.0.0 in GCP. All the controls are mapped to misconfiguration policies for your regulatory requirements.
Brace yourself for what’s coming up next:
- IAM Right sizing for GCP & AWS
- ISO 27002 compliance support
- DigitalOcean CSPM & 1-Click Kubernetes integration
Industry News
Security for your Code, Cloud and Data
Cloudanix replaces your 5-6 disjointed security tools within 30 minutes.
Get StartedBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read MoreThursday, Feb 05, 2026
CSPM vs. CNAPP: Navigating Cloud Security Evolution for Modern Enterprises
The shift to cloud-native architectures represents a fundamental change in how applications are designed, built, and dep
Read MoreThursday, Jan 22, 2026
Top 10 Identity and Access Management Solutions
Identity and Access Management (IAM) has traditionally been considered one of the boring parts of security. But with the
Read More