The digital landscape, once a frontier of innovation, rapidly transformed into a battleground. As web applications proliferated, so did the vulnerabilities lurking within their code. In the nascent days of the internet, security was often an afterthought, a patch applied after a breach.
Early websites, simple and static, rarely faced sophisticated attacks. However, as applications grew complex, incorporating dynamic content and user interaction, the cracks began to show. The rise of e-commerce, online banking, and social media introduced sensitive data into the equation, making applications prime targets for malicious actors. SQL injection, cross-site scripting (XSS), and buffer overflows emerged as potent threats, exposing the fragility of the “build now, secure later” approach. This realization spurred the development of systematic methods for identifying and mitigating vulnerabilities before they could be exploited, marking the genesis of Application Security Testing (AST).
What is Application Security Testing?
Application Security Testing (AST) is a set of processes, tools, and methodologies designed to identify and address security vulnerabilities within software applications. Essentially, it’s a proactive approach to safeguarding applications from potential attacks. Unlike traditional security measures that focus on network perimeters, AST delves into the application’s code, architecture, and runtime environment. It aims to detect flaws that could compromise confidentiality, integrity, and availability
AST encompasses a range of techniques, including static application security testing (SAST), dynamic application security testing (DAST), interactive application security testing (IAST), and software composition analysis (SCA). Each method offers unique insights into different aspects of application security, from analyzing source code to simulating real-world attacks. By integrating AST into the software development lifecycle (SDLC), organizations can build more resilient applications, minimizing the risk of costly data breaches and reputational damage.
What are the types of Application Security Testing?
In the complex world of application security, a variety of testing methodologies exist, each designed to uncover different types of vulnerabilities. Understanding these methods is crucial for building robust and secure applications. Here’s a breakdown of the core types of Application Security Testing, exploring their unique approaches and strengths.
1. Static Application Security Testing (SAST)
SAST analyzes an application’s source code without executing it. It scans for coding flaws, such as buffer overflows or SQL injection vulnerabilities, by examining the code’s structure and syntax. It is a white-box testing technique, meaning it requires access to the source code, and is typically performed early in the SDLC. Think of it as a code grammar checker, but for security. It reads your application’s code like a book, looking for common mistakes that could lead to vulnerabilities, without actually running the program.
2. Dynamic Application Security Testing (DAST)
DAST simulates real-world attacks by interacting with a running application. It probes for vulnerabilities like cross-site scripting (XSS) or authentication flaws by sending various inputs and observing the application’s responses. It is a black-box testing technique, meaning it doesn’t require access to the source code.
This method acts like a hacker trying to break into your application. It runs the application and throws different inputs at it to see if it crashes or reveals sensitive data, simulating real-world attacks.
3. Interactive Application Security Testing (IAST)
IAST combines elements of SAST and DAST. It analyzes application behavior during runtime by instrumenting the application. This allows for real-time vulnerability detection with better accuracy than DAST, as it has insight into the application’s internal workings. It provides developers with immediate feedback.
Imagine a security guard watching your application while it’s running. It combines the code analysis of SAST with the runtime testing of DAST, giving a more accurate picture of potential weaknesses.
4. Software Composition Analysis (SCA)
SCA focuses on identifying vulnerabilities in open-source components used within an application. It analyzes the application’s dependencies and checks for known security flaws in those components. This is crucial because many modern applications rely heavily on third-party libraries.
Because most applications use pre-built software parts (like Lego bricks), SCA checks these parts for known security problems. It’s like checking the safety record of the building materials you’re using.
There are a few other types of application security testing, although they are less commonly discussed than the core four. Let’s explain them in a similar, easy-to-understand way:
5. Mobile Application Security Testing (MAST)
This focuses specifically on apps for phones and tablets. It checks for issues like data leaks, insecure storage, and vulnerabilities in how the app interacts with the device’s operating system. It’s like a specialized security check for your mobile app.
6. API Security Testing
APIs (Application Programming Interfaces) are how different software systems talk to each other. This testing checks if those communication channels are secure, looking for things like unauthorized access or data manipulation. It’s like making sure the messages being sent between applications are safe.
7. Runtime Application Self-Protection (RASP)
Unlike other testing methods, RASP is a security technology built directly into the application. It actively monitors the application during runtime and blocks attacks as they happen. It’s like having a built-in security guard that reacts instantly to threats.
8. Fuzzing
Fuzzing involves bombarding an application with random, unexpected inputs to see if it crashes or behaves erratically. This helps uncover unexpected vulnerabilities that might not be found through other methods. It is like shaking a product to see if any parts fall off.
By implementing a combination of these AST techniques throughout the Software Development Lifecycle (SDLC), organizations can achieve a comprehensive security posture. Each method plays a vital role in identifying and mitigating potential threats, ultimately contributing to the development of safer and more resilient applications in today’s increasingly volatile digital environment.
What are the 3 core testing methodologies?
Understanding the ‘color’ of your testing approach is critical in application security. Black-box, gray-box, and white-box testing represent distinct methodologies, each offering unique perspectives on an application’s security posture. By strategically employing these techniques, security professionals can achieve a comprehensive and nuanced assessment of potential vulnerabilities.
Black-box Testing
This method treats the application as a closed box. Testers interact solely with the user interface, providing inputs and analyzing outputs, without any knowledge of the underlying code. It simulates real-world attacks, focusing on functionality and potential vulnerabilities from an external user’s perspective. It helps identify issues related to user input validation and runtime behavior.
Gray-box Testing
Gray-box testing involves partial knowledge of the application’s internal structure. Testers understand the application’s architecture and data flow but may not have complete access to the source code. This approach allows for targeted testing, focusing on specific components and interactions, balancing efficiency and thoroughness. It is very useful for testing APIs.
White-box Testing
White-box testing grants testers full access to the application’s source code, architecture, and internal workings. This enables detailed analysis of code logic, data flow, and potential vulnerabilities within the application’s structure. It is a very effective tool for finding code-level vulnerabilities, and allows for the earliest possible detection of issues.
The choice between black-box, gray-box, and white-box testing depends on the specific security goals, available resources, and the stage of the software development lifecycle. Often, a combination of these approaches provides the most robust and effective security assessment, ensuring a well-rounded defense against potential threats.
What are the best practices for Application Security Testing?
Regardless of size or stage, every organization developing applications faces the critical imperative of robust security testing. While the scale and resources may differ, the fundamental principles remain consistent. From the established enterprises with complex infrastructures to the agile startups building their MVPs, a strategic approach to Application Security Testing (AST) is paramount.
Let’s explore best practices tailored to each context, ensuring that security is not just a feature, but a foundational element.
Best practices tailored for large and mid-sized organizations
- Integrate AST into the SDLC (Shift Left): This “shift left” approach enables early detection and remediation of vulnerabilities, reducing costs and delays associated with fixing issues later in the development process. Automated SAST scans during code commits and DAST/IAST during testing phases are key.
- Prioritize and automate: With numerous applications and frequent updates, prioritize testing based on risk. Automate repetitive testing tasks using CI/CD pipelines to ensure consistent and efficient security assessments. Focus on automating DAST and SAST scans, and integrating SCA to keep a constant check on open-source libraries.
- Employ a hybrid testing approach: Don’t rely on a single AST method. Combine SAST, DAST, IAST, and SCA to achieve comprehensive coverage. SAST identifies code-level flaws, DAST simulates real-world attacks, IAST provides runtime insights, and SCA manages open-source risks. This multi-layered strategy minimizes blind spots.
- Establish a centralized vulnerability management system: Implement a system to track, prioritize, and remediate vulnerabilities identified during AST. This system should integrate with development tools and provide clear reporting and metrics. It is critical that all vulnerabilities are tracked and that remediation actions are also tracked.
- Provide Security training and awareness: Educate developers, testers, and security teams on secure coding practices and common vulnerabilities. Regular training and awareness programs foster a security-conscious culture, reducing the likelihood of introducing new vulnerabilities. This is an essential practice, as developers who understand security are less likely to produce vulnerable code.
- Continuous monitoring and feedback loops: Security testing should not be a one-time event. Implement continuous monitoring and feedback loops to identify and address emerging threats. Use RASP for real-time protection, and gather data from production environments to refine testing strategies. This closes the loop of development, testing, and production.
Best practices tailored for small-sized organizations and startups
Let’s tailor application security testing best practices specifically for small organizations and startups, considering their unique constraints and priorities.
- Focus on essential vulnerabilities first: Startups often have limited resources. Prioritize testing for critical vulnerabilities that pose the highest risk, such as SQL injection, XSS, and authentication flaws. Utilize free or low-cost SAST and DAST tools to gain initial visibility. Concentrate on the most likely attack vectors.
- Leverage open-source and community tools: Embrace open-source security testing tools and community resources. Many excellent, free options exist for SAST, DAST, and SCA. Utilize community forums and online resources for guidance and support. This helps to reduce the spending on expensive tools.
- Integrate security into the Minimum Viable Product (MVP): Incorporate basic security testing into the MVP development process. Even in early stages, address fundamental security concerns to avoid costly refactoring later. This prevents the need to rebuild from the ground up.
- Automate basic security checks: Automate simple security checks within the development workflow. This can include basic SAST scans during code commits and automated DAST scans on deployed builds. Use CI/CD tools to automate these processes.
- Prioritize third-party security audits: If resources are extremely limited, consider occasional third-party security audits. These audits can provide an external perspective and identify critical vulnerabilities that internal teams might miss. This is very effective for getting a birds-eye view of the application’s security.
- Build a security-aware culture early: Foster a security-conscious culture from the outset. Educate all team members on basic security principles and best practices. Even basic training can prevent many common vulnerabilities. This is an investment that pays dividends in the long run.
Whether you’re a large organization implementing a comprehensive security program or a startup laying the groundwork for future growth, integrating AST into your development lifecycle is non-negotiable. By adapting these best practices to your specific needs, you can mitigate risks, build trust, and ensure the long-term security and resilience of your applications. In today’s threat landscape, proactive security testing is not a luxury, but a necessity for every organization, regardless of size.
What are the top three common challenges that organizations face in application security testing?
Navigating the complexities of application security testing presents unique hurdles for mid-sized and large organizations. The sheer scale of their application portfolios, the integration of security into established workflows, and the relentless evolution of cyber threats create a formidable landscape. However, by proactively addressing these challenges with strategic solutions, organizations can fortify their defenses and build resilient applications.
Managing the scale and complexity of applications
Large organizations often have a vast portfolio of applications, many of which are complex and interconnected. Maintaining consistent security testing across all these applications can be overwhelming. The constant release cycles and frequent updates further exacerbate this challenge.
Here are a few solutions that one can try:
- Implement a centralized vulnerability management platform to track and prioritize findings from all applications.
- Automate testing processes using CI/CD pipelines and integrate AST tools into the development workflow.
- Adopt a risk-based approach to prioritize testing efforts, focusing on critical applications and high-risk vulnerabilities.
- Establish clear ownership and accountability for application security across development teams.
Integrating security into existing development processes
Many large organizations have established development processes that may not have security deeply ingrained. Introducing AST into these processes can face resistance from development teams, leading to delays and inconsistencies.
Here are a few solutions that we recommend:
- Foster a security-first culture through training and awareness programs for developers and other stakeholders.
- Provide clear guidelines and best practices for secure coding and testing.
- Integrate AST tools seamlessly into existing development tools and workflows.
- Establish security champions within development teams to advocate for security best practices.
- Create policies that mandate security testing.
Keeping pace with evolving threats and technologies
The threat landscape is constantly evolving, with new vulnerabilities and attack vectors emerging regularly. Organizations struggle to keep their security testing practices up-to-date. Additionally, the adoption of new technologies like cloud computing and microservices introduces new security challenges.
The possible solutions to this challenge include:
- Invest in continuous security training and education for security teams.
- Implement continuous monitoring and feedback loops to identify and respond to emerging threats.
- Adopt a flexible and adaptable security testing strategy that can accommodate new technologies and threats.
- Use RASP and other runtime protection tools.
- Perform regular penetration testing by 3rd parties.
Overcoming these challenges requires a holistic and adaptable approach. By embracing automation, fostering a security-centric culture, and staying abreast of emerging threats, organizations can effectively manage application security testing at scale. Ultimately, a proactive and strategic approach to AST is essential for protecting valuable assets and maintaining trust in today’s dynamic digital environment.
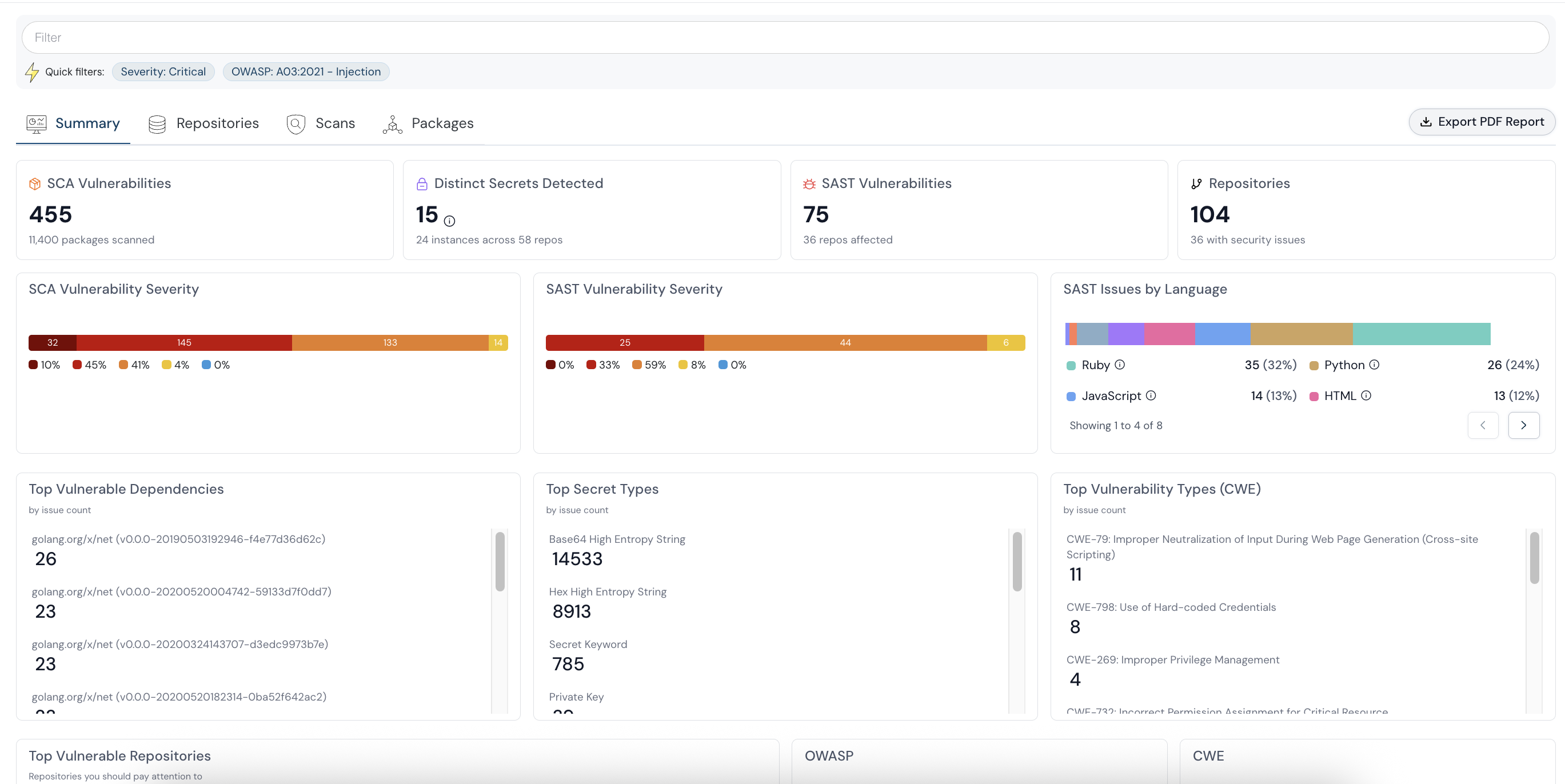
Application Security Testing with Cloudanix
Cloudanix streamlines your security posture by integrating SAST, DAST, and SCA into a unified platform. By automating vulnerability management across your CI/CD pipeline, Cloudanix helps organizations “shift left,” ensuring resilient, compliant applications without slowing down development.
Conclusion
In the ever-evolving digital ecosystem, Application Security Testing (AST) stands as an indispensable shield against potential cyber threats. From the foundational principles of SAST, DAST, IAST, and SCA to the strategic implementation of black-box, gray-box, and white-box testing methodologies, organizations must prioritize proactive security measures. Whether a sprawling enterprise or a nimble startup, the adoption of tailored best practices and the diligent navigation of common challenges are paramount. By embracing a comprehensive AST strategy, businesses can fortify their applications, safeguard sensitive data, and cultivate a culture of security, ensuring resilience in the face of an increasingly complex threat landscape.
Correlate security findings from PR to runtime >>
