Databases hold the crown jewels. They contain the highly sensitive customer records, financial figures, and intellectual property that are the lifeblood of your business and the primary target for malicious actors. Managing access to these systems is the single biggest challenge for security teams, DBAs, and compliance officers alike.
The Database Privilege Dilemma
Traditional security models rely on permanent standing privileges for Database Administrators (DBAs) and data analysts. A DBA needs elevated access for schema migrations or performance tuning, and a data analyst needs read access for crucial reports.
The problem is simple: Permanent access creates massive, persistent risk.
- The Compliance Nightmare: Regulations like GDPR, HIPAA, and PCI DSS demand proof of Least Privilege. When auditors ask, “Who accessed PII data and why?”, answering requires days of manual log collection and reconciliation across disparate systems. As one customer noted: “Our user access review is now 1 click away instead of multiple people working for multiple days collecting logs of information.”
- The Data Granularity Gap: Traditional Privileged Access Management (PAM) often stops at the database server level. This grants users access to the entire database—all tables and all actions—violating the Just Enough Privilege (JEP) principle and dramatically expanding the blast radius of a potential breach.
- Multi-Environment Chaos: In today’s hybrid world, a company might use PostgreSQL on-prem, AWS RDS, Azure SQL Database, and MongoDB in a self-hosted cluster. Managing policies across this mix of cloud-native managed services and self-hosted instances leads to policy fragmentation and security gaps.
Our JIT Solution: Ultimate Granularity and Control
Our Just-in-Time (JIT) solution is specifically engineered to eliminate these challenges by transitioning access from static roles to dynamic, temporary, and tightly controlled sessions.
Universal Database Coverage
Cloudanix provides unified JIT access control across your entire data landscape, supporting all major relational and NoSQL technologies, including:
- MySQL
- PostgreSQL
- Oracle
- SQL Server
- MongoDB
- Cassandra
Crucially, this support extends seamlessly to both cloud-native managed databases (e.g., AWS RDS, Azure SQL) and self-hosted databases deployed on-prem or within IaaS environments.
The Power of Precision: Granular Access Policies
Cloudanix brings the Just Enough Privilege (JEP) principle directly to the database layer, allowing for unparalleled policy granularity:
- Resource Level: Target specific databases, schemas, tables, views, and stored procedures.
- Action Level: Restrict access to specific actions (e.g., SELECT only, INSERT, UPDATE, DELETE).
- Data Level: Enforce Row-Level Security (RLS), restricting a user’s access to specific rows of data (e.g., a regional analyst can only view customer data from their specific region).
This level of control ensures that a DBA receives exactly the access they need, for the minimum time required, and nothing more.
Frictionless Access and Modern Credential Management
Security should never impede legitimate work. Our JIT solution focuses on operational efficiency to make access secure, yet frictionless for users.
Zero-Standing Credentials and Dynamic Provisioning
Cloudanix eliminates the need for permanent, shared, or hard-coded database passwords:
- Authentication: The solution leverages existing IAM credentials (the user’s identity) to authenticate the request.
- Provisioning: For tools that require traditional connection methods, the system dynamically generates temporary database passwords on demand.
- Hygiene: Credentials are automatically rotated and invalidated once the JIT session expires, ensuring no privileged credentials are ever left exposed.
Streamlined Workflows and the Single-Task Advantage
- Flexible Connections: Users can access the database using their preferred tools—whether through a command-line interface (CLI) or desktop clients (like DBeaver).
- Integrated Request Workflow: We integrate directly with established ticketing systems like Jira and ServiceNow to automatically trigger, justify, and approve JIT access requests based on existing DBA.
- Single-Task Scoping: Our platform uniquely handles complex requests that span resource types. For example, a single JIT request can grant a user temporary access to a production MySQL instance and the associated S3 bucket holding its backups, ensuring the entire task can be completed within a secure, time-bound session.
The Compliance Differentiator: SQL-Level Auditing
This is where our JIT solution transforms security compliance from a manual burden into an automated strength.
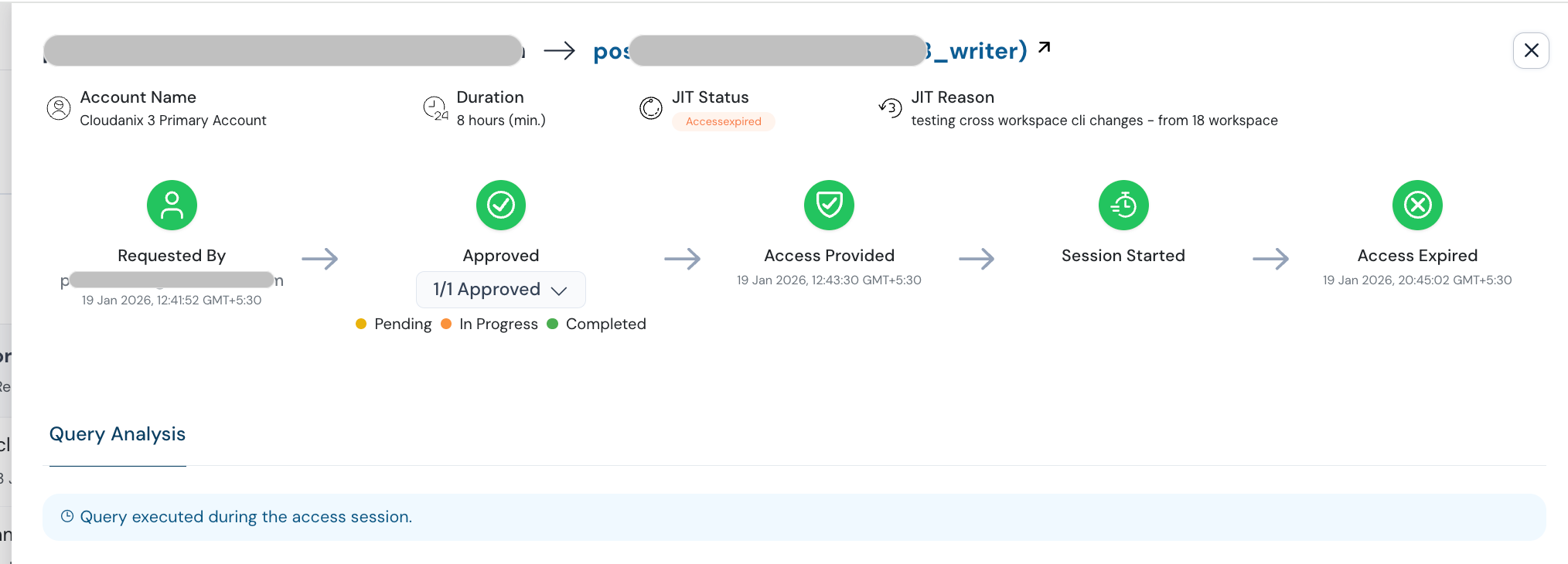
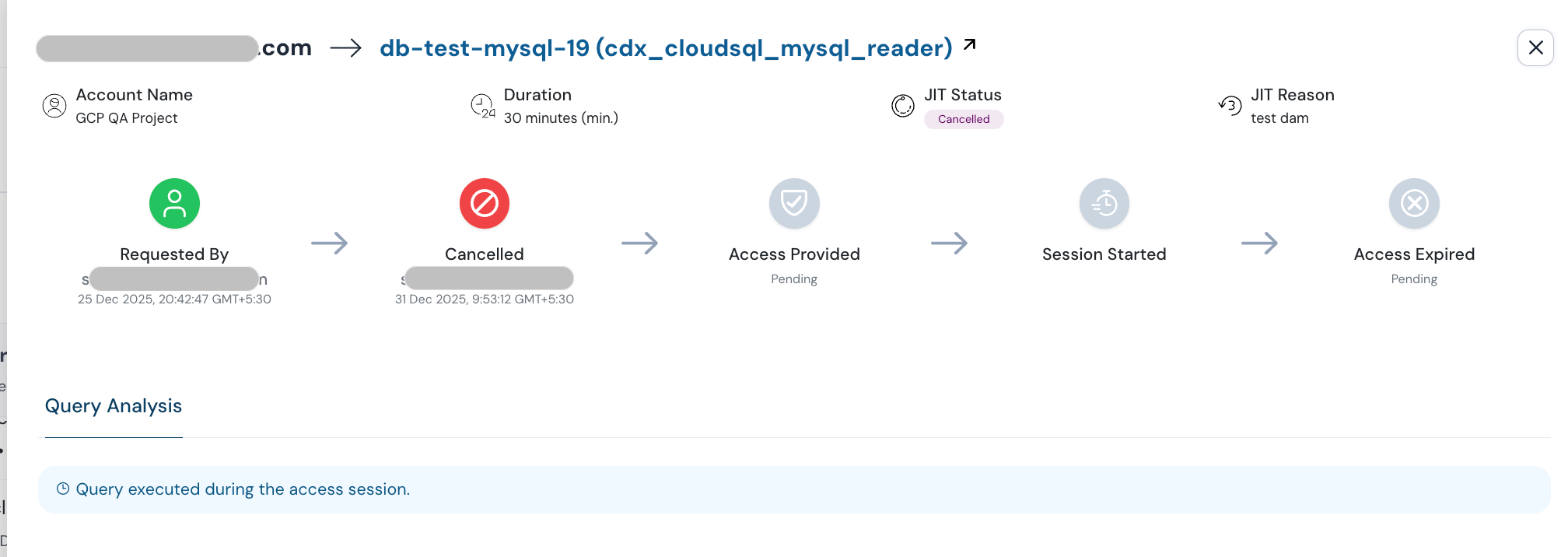
Forensic-Level Audit Trails
The key differentiator is our deep visibility into the session. We don’t just log the connection event; we log individual SQL queries executed by the user during the JIT session. This forensic level of detail eliminates ambiguity and provides irrefutable evidence of all actions taken while privileged.
Real-Time Monitoring and Compliance-Ready Reports
- Real-Time Security: The system provides built-in real-time monitoring of database activity during the JIT session, enabling security teams to detect and terminate suspicious queries instantly.
- Targeted Reporting: Generate actionable reports specifically designed for auditors and security teams:
- Reports detailing all DELETE or UPDATE queries.
- Reports tracking PII data access across all connected data sources.
- Reports on the top tables accessed during a specific audit period.
Conclusion: Simplified Security and the 1-Click Audit
Our Just-in-Time Access platform for Database Administration and Sensitive Data is more than a control mechanism—it’s a unified security platform.
By delivering unprecedented granularity (down to RLS), modern credential management (IAM/Temp Passwords), and comprehensive SQL-level auditing across a multi-database, hybrid environment, we allow businesses to move beyond the security vs. productivity trade-off.
You eliminate standing privileges, drastically reduce your attack surface, and, most importantly, you simplify your most complex compliance obligations.
Learn how to eliminate standing privileges, simplify your next compliance audit, and provide the most secure, compliant access to your most sensitive data. Schedule a demo today!
