IAM JIT, PagerDuty Integration, Image scanning with Jenkins and Bitbucket
The most in demand security feature across the globe has now been shipped. Take a guess, it gives you super powers…still not sure then read along to see what I’m talking about.
Cloudanix joins AWS ISV Accelerate program, read about it here.
Just In Time Access
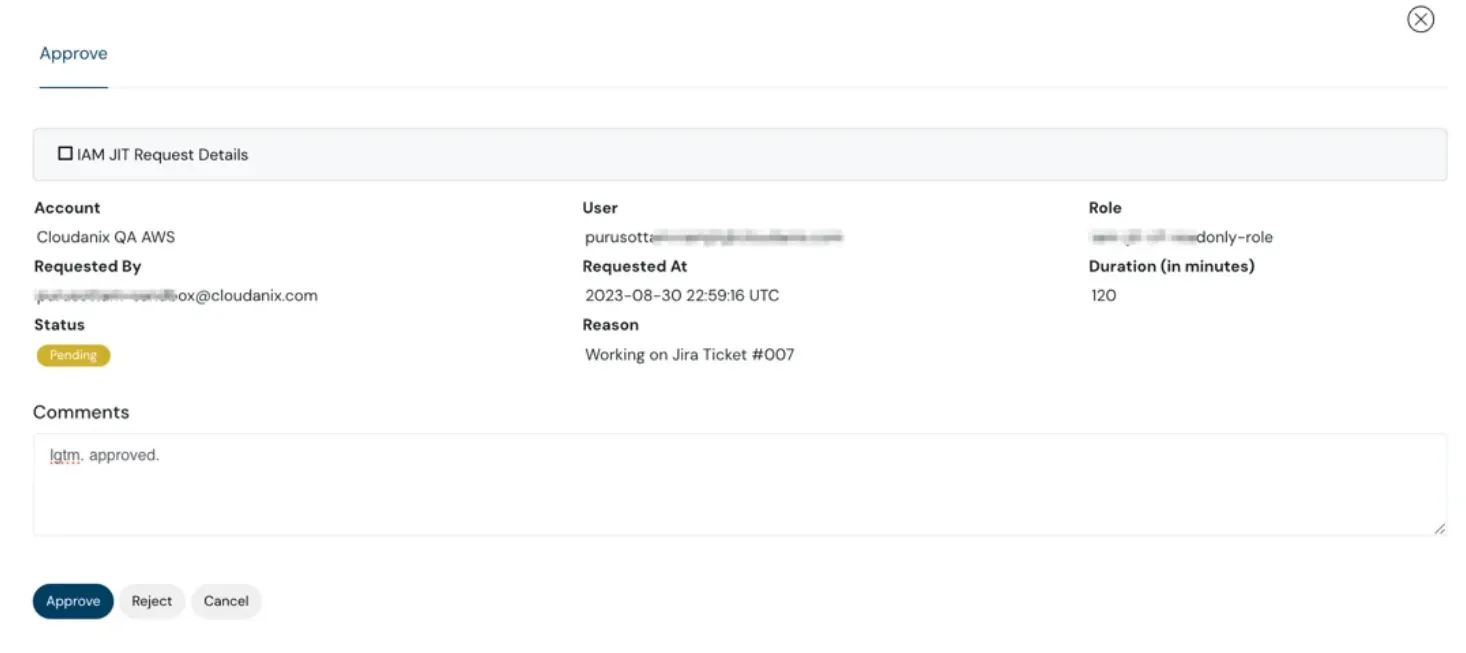
Instead of Just In Case Access, now your team can request elevated privileges for Just In Time Access. With in-built workflows, you have the super power to follow Principles of Least Privilege without any effort. Cloudanix takes care of Providing Access, Revoking Access and Auditing the Access.
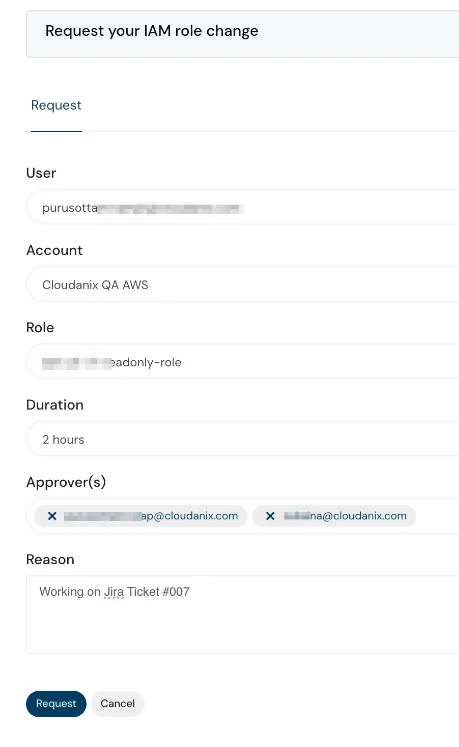
IAM JIT Access dashboard
IAM JIT Access request dashboard
 IAM JIT view dashboard
IAM JIT view dashboard
 IAM JIT overview dashboard
IAM JIT overview dashboard
PagerDuty Integration
Arm your on-call team with additional context from Cloudanix. Integrate Cloudanix with PagerDuty to push Security Alerts to PagerDuty Services.
 Global search feature in dashboard
Global search feature in dashboard
 Global search feature detailed view in dashboard
Global search feature detailed view in dashboard
Graph View of Attack Path and Connected Assets
It’s not enough to see an asset information without its related assets and also, if there’s an attack path that can be exploited. With the connected assets view, you can do both. You can expand this further by clicking on any node and see its connected assets as well.
 PagerDuty settings - dashboard
PagerDuty settings - dashboard
 Cloudanix and PagerDuty integration
Cloudanix and PagerDuty integration
 Cloudanix and PagerDuty integration
Cloudanix and PagerDuty integration
Image Scanning at Build Time with Jenkins and Bitbucket
We have extended Image Scanning capability to Jenkins and Bitbucket as well. With a few clicks, integrate Image Scanning in your pipelines. With our Plugins, findings are presented at both the Pipeline and in the Cloudanix Console.
Threat Detection for GitHub & Bitbucket
Similar to our Threat Detection for Clouds (AWS, GCP & Azure), we have added Threat Detection capabilities to GitHub and Bitbucket. We cover over 30 threats ranging from License Changes to Repository Status changes and many more.
AWS Startup Security Baseline Compliance Pack
AWS Startup Security Baseline (SSB) is a set of controls that create a minimum foundation for businesses to build securely on AWS without decreasing their agility. We have built a Compliance Pack for Startups to visualize the Security Posture of the foundation.
Kubernetes Support for Pod Security Standards instead of Pod Security Policies
Pod Security Policies (PSP) were officially deprecated and replaced with Pod Security Admission (PSA) in Kubernetes version 1.21. It implements Pod Security Standards (PSS), policies to cover a broad security spectrum. In 1.25, PSP was completely removed. So, we have updated our charts to support PSAs.
Here’s a migration guide: https://kubernetes.io/docs/tasks/configure-pod-container/migrate-from-psp/
Additional Resources
- Importance of Kubernetes Security
- How to go about building a SAST plan for your company?
- What is Vulnerability Management?
- What is Threat Modeling?
Industry News
- Build Docker Images Smaller and Secure
- Kubernetes 1.28 (Planternetes) is out
- Understand LLMs and the threats they pose
TODO:// is not an option for Cloud Security
Security for your Code, Cloud and Data
Cloudanix replaces your 5-6 disjointed security tools within 30 minutes.
Get StartedBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read MoreThursday, Feb 05, 2026
CSPM vs. CNAPP: Navigating Cloud Security Evolution for Modern Enterprises
The shift to cloud-native architectures represents a fundamental change in how applications are designed, built, and dep
Read MoreThursday, Jan 22, 2026
Top 10 Identity and Access Management Solutions
Identity and Access Management (IAM) has traditionally been considered one of the boring parts of security. But with the
Read More