Incident Response
Detect, Contain, Eradicate, and Recover
Before diving deep into the topic, let us understand the basics of security incidents. A security incident is any event (digital or physical) that actually or potentially compromises the confidentiality, integrity, or availability of information or an information system.
Security incidents are not always intentional attacks; they can also result from unintentional violations of security policies by authorized users inside the organization.
The CIA Triad
The Confidentiality, Integrity, and Availability (CIA) triad is a model used to guide information security policies.
- Confidentiality: Information is only accessible to authorized individuals.
- Integrity: Ensures accuracy and trustworthiness of data.
- Availability: Ensures reliable access to information and systems when needed.
Examples of Security Incidents:
- Data breaches
- Denial-of-Service (DoS) attacks
- Malware infections
- Phishing attacks
- Insider threats
What is Incident Response?
Incident response is a structured process to detect, contain, eradicate, and recover from a security incident. It includes people, processes, and technologies that enable organizations to address cyber threats proactively.
“Cloud security and product security are mostly going to be focused on the preventative controls. What can we do to stop something from happening?”
— Pablo Vidal, ScaleToZero Podcast
All key processes are usually documented in an Incident Response Plan (IRP).
According to IBM, the global average cost of cyber attacks rose to USD 4.5 million in 2023.
Common Challenges in Detecting and Responding to Incidents
1. Evolving Threat Landscape
- Cybercriminals adopt new techniques faster than defenders can react.
- Zero-day exploits and Advanced Persistent Threats (APTs) remain hard to detect.
2. Lack of Visibility and Monitoring
- Legacy systems or IoT devices may remain unmonitored.
- Log overload makes spotting true anomalies difficult.
- Shadow IT introduces unapproved risks.
3. Resource Constraints
- Shortage of skilled professionals.
- Budget limitations hinder tooling and training.
- Alert fatigue causes security teams to miss critical alerts.
4. Slow Detection & Response Times
- Manual triaging delays containment.
- Dwell time (time taken to detect incidents) allows deeper damage.
- Lack of decision-making frameworks.
5. Communication and Collaboration Gaps
- Poor coordination across teams.
- Delayed or inadequate external notifications.
- Undefined responsibilities in IR teams.
6. Insider Threats
- Malicious insiders may misuse access intentionally.
- Negligent insiders can trigger breaches via careless actions.
5 Key Steps of a Secure Incident Response Process
1. Preparation
- Build a clear IRP with roles, communication flows, and mitigation steps.
- Train security and engineering teams.
- Conduct tabletop simulations to test readiness.
2. Detection and Identification
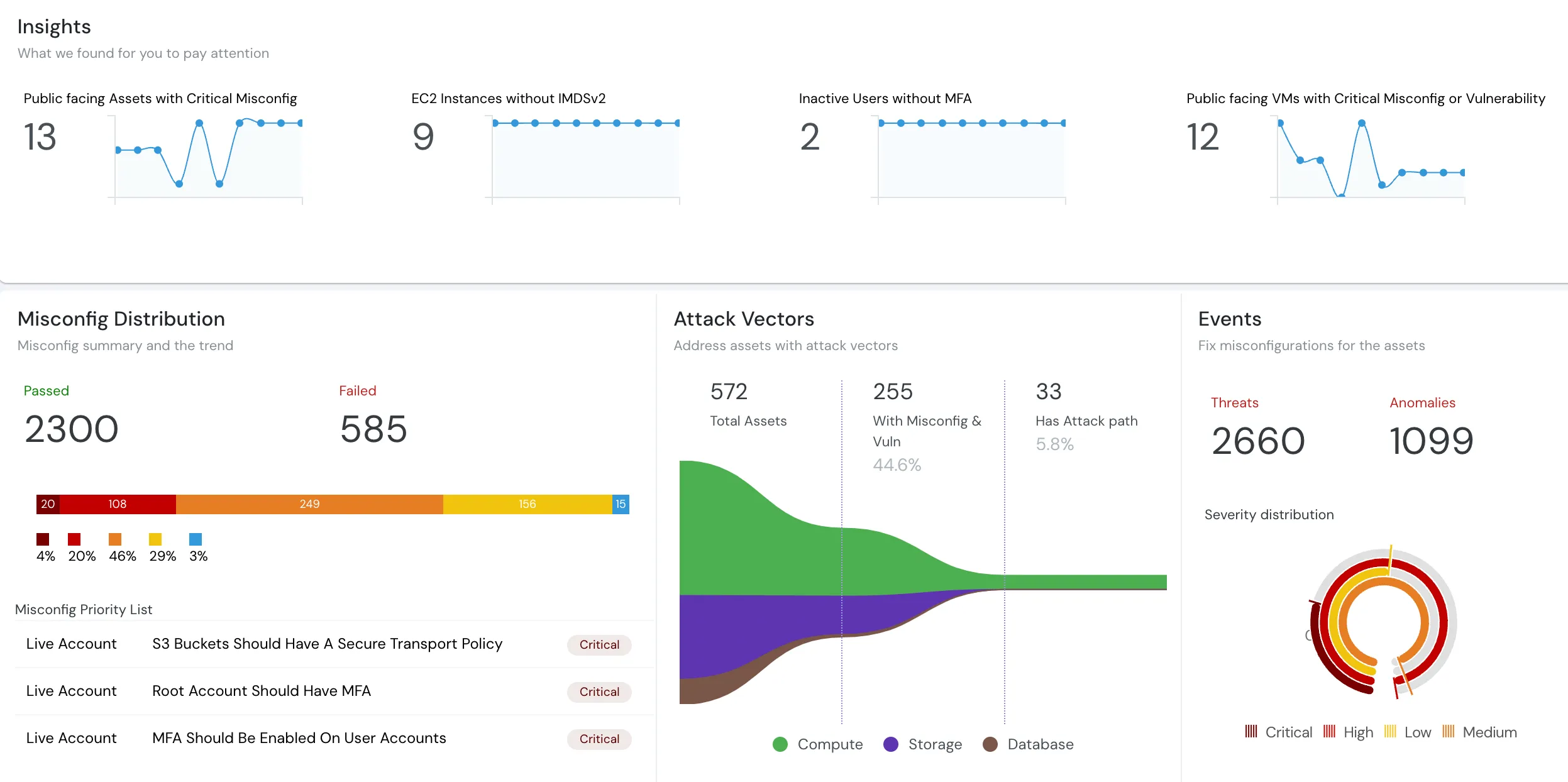
- Use SIEMs, CNAPPs, and firewall logs to monitor behavior.
- Analyze logs regularly.
- Encourage employees to report suspicious activity.
3. Containment
- Short-term: Immediately isolate affected devices.
- Long-term: Patch systems, enhance monitoring, disable compromised accounts.
4. Eradication
- Investigate root causes through forensics.
- Remove malware, close exploited vulnerabilities, and rotate credentials.
5. Recovery
- Restore systems using clean backups.
- Conduct a post-incident review to document lessons learned and improve IRP.
Expert Advice: Simplified IR Flow by Pablo Vidal
From a ScaleToZero podcast episode, Pablo shared a concise structure for IR:
- Detection and Reporting: Anyone can report suspicious behavior.
- Initial Review: IR team validates the report.
- Investigation: Scope, origin, and method are analyzed.
- Prioritization: Urgency and impact determine resource allocation.
- Response Flowchart:
- Right team involvement
- Action steps
- Containment plan
- External collaboration if required
Role of Automation Tools in Incident Response
Automation reduces load on security professionals:
- Auto-creates IR folders and documentation.
- Sets up communication workflows.
- Runs predefined response playbooks.
- Prioritizes alerts based on severity.
By automating repetitive tasks, human teams can focus on strategic decision-making and investigation.
Is Generative AI Reshaping Incident Response?
While early in its adoption curve, GenAI shows promise in:
Log Schema Inference
- AI models analyze sample logs to infer structure, easing integration of new sources.
Auto-Knowledgebase Assistant
- Security chatbots answer internal questions using Confluence-like documentation.
- Reduces human effort spent on repetitive queries.
Generative AI is expected to improve efficiency while reducing operational stress on security teams.
People Also Read
- What is Threat Modeling?
- What is Vulnerability Management?
- What is Zero Trust Security?
- Third Party Risk Management
